Penetration Tests
Years of experience
CVE's

About me
As an independent security researcher and information security professional I have long-standing experience in the field of audits and penetration tests. I started my career in IT security in 2016, as a penetration tester for a German consulting company specialized in cybersecurity. Since 2018, I have been working as a freelance penetration tester and security researcher. I have an interest in presenting my security research and I have spoken in several international security conferences, such as CanSecWest, SecTor, DeepSec, TyphoonCon and BSides Budapest. My formal education includes a Master of Science in IT security.
Certifications:
- Offensive Security Certified Professional (OSCP)
- Offensive Security Wireless Professional (OSWP)
- Microsoft Cybersecurity Architect (SC-100)
- Microsoft Azure Security Engineer (AZ-500)
My services
My goal is to identify potential vulnerabilities before cyber criminals do with malicious intent. Through my services, I would like to support you in addressing vulnerabilities and thus improve the security level of your application or network infrastructure.
- Individual security analysis according to your needs
- Manual in-depth security analysis supported by tools and vulnerability scanners
- In compliance with audit standards such as ASVS and OWASP Top 10
- Professional report in German or English
- Risk classification, recommendation for remediation and management summary
- Fully independent and expert advice
Please don't hesitate to contact me for a free consultation, a list of references or an example report.

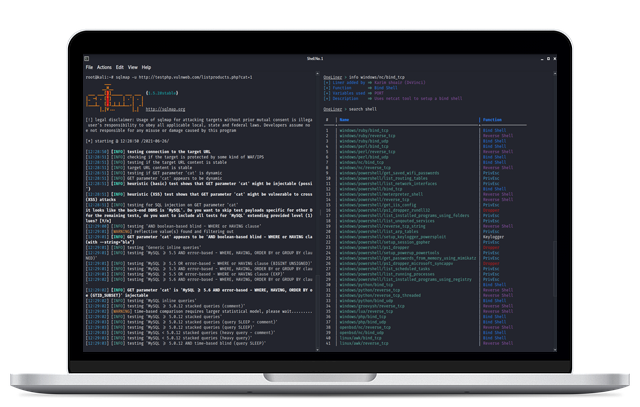
Application Security
Penetration test of your web application, API or native desktop application. The aim is to identify vulnerabilities and security-relevant misconfigurations in the application itself, its framework, and the underlying server.
- Web applications
- APIs, e.g. REST or SOAP services
- Native desktop applications

Infrastructure Assessment
Security analysis of a companies internal IT infrastructure or Internet facing systems. This way, a hacker is simulated trying to break into your corporate network.
- Identification & analysis of network services
- Discovery of vulnerabilities, misconfigured services and lack of security hardening
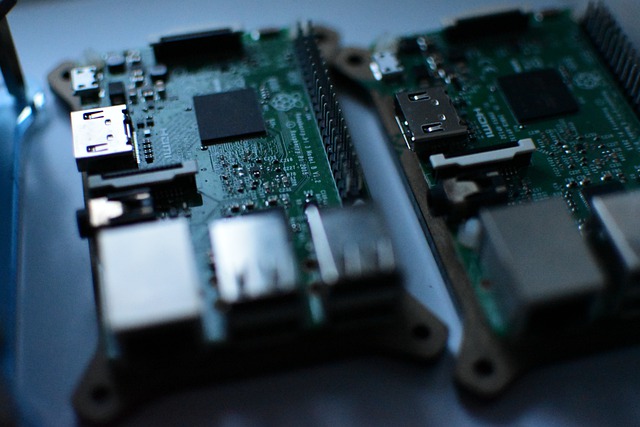
IoT Security
Security assessment of IoT devices, their interfaces as well as firmware analysis.
- In-depth analysis of the device's network services
- Analysis of device interfaces, such as Ethernet, WiFi, Bluetooth or ZigBee
- Static firmware analysis
Contact
Contact Me
I want to help you address your cybersecurity concerns and challenges while you focus on core business. Please don't hesitate to contact me for a free consultation, a list of references or an example report.